In today’s complex and ever-evolving digital landscape, high-security IT environments face unique challenges. Organizations handling sensitive data, such as government agencies, financial institutions, and healthcare providers, require robust security measures to protect against cyber threats and maintain compliance with stringent regulations. Customer Relationship Management (CRM) and Remote Monitoring and Management (RMM) systems are essential tools for these organizations, but their implementation and management must be carefully considered to avoid introducing vulnerabilities.
The integration of CRM and RMM offers numerous benefits, including streamlined operations, improved customer service, and enhanced security posture. However, these benefits can only be realized if the systems are properly configured and secured. A failure to address security concerns can expose sensitive data to unauthorized access, leading to data breaches, financial losses, and reputational damage. Therefore, understanding the security implications of CRM and RMM is crucial for organizations operating in high-security IT environments.
This article provides a comprehensive overview of CRM and RMM in the context of high-security IT environments. We will explore the key security considerations for each type of system, discuss best practices for implementation and management, and highlight the importance of a holistic security approach. By understanding these principles, organizations can leverage the power of CRM and RMM while maintaining the highest levels of security and compliance.
Understanding the Landscape: CRM and RMM Defined
Before diving into the security aspects, it’s important to define CRM and RMM and their respective roles in a high-security IT environment.
Customer Relationship Management (CRM)
CRM systems are designed to manage and analyze customer interactions and data throughout the customer lifecycle, with the goal of improving business relationships, assisting in customer retention, and driving sales growth. In high-security environments, CRM systems often contain sensitive customer data, including Personally Identifiable Information (PII), financial records, and health information. Examples of CRM systems include Salesforce, Microsoft Dynamics 365, and SugarCRM. The security of this data is paramount and must be protected through robust access controls, encryption, and monitoring.
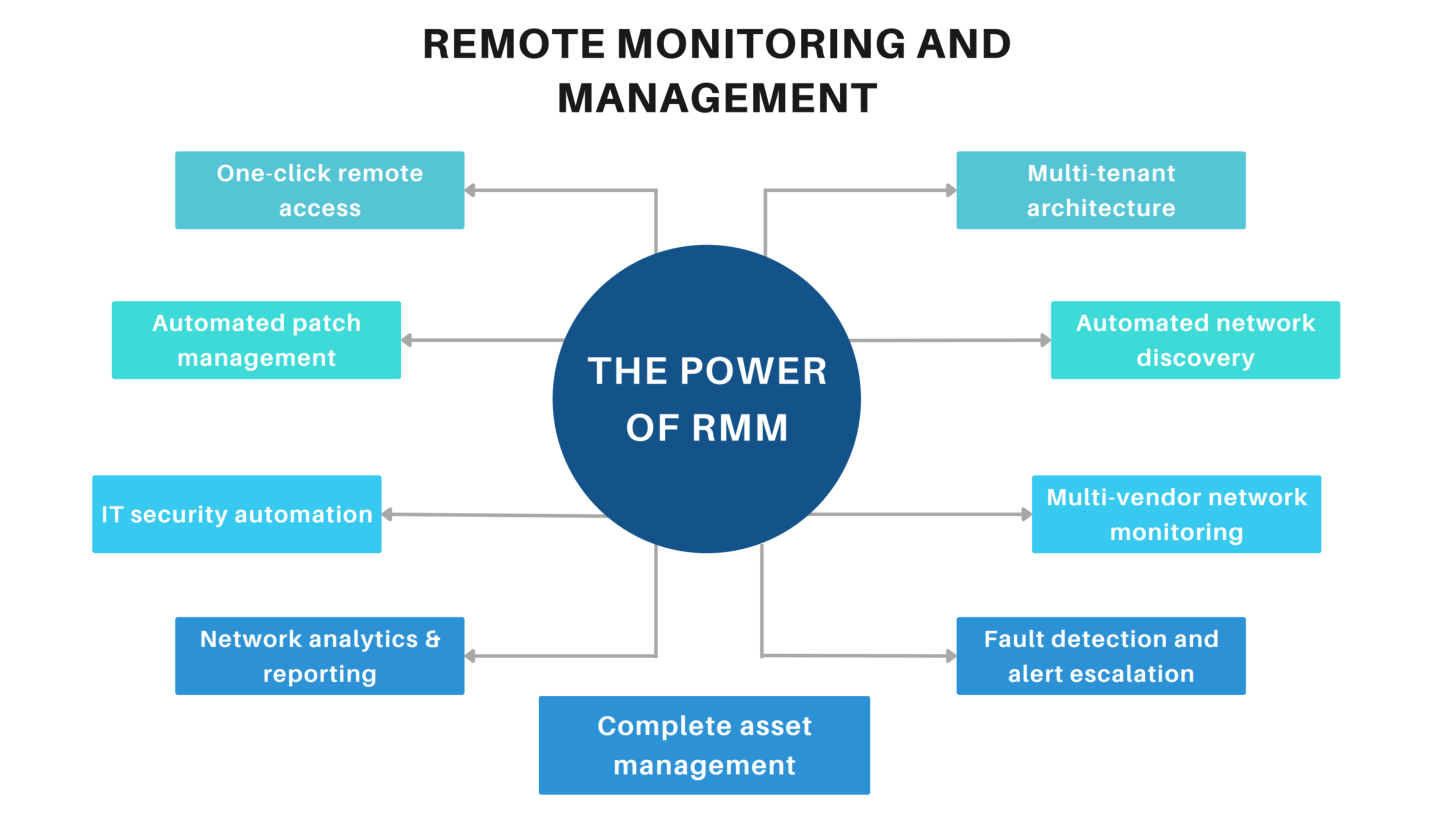
Remote Monitoring and Management (RMM)
RMM systems are used by IT service providers and internal IT departments to remotely monitor and manage client endpoints, networks, and servers. They provide real-time visibility into the health and performance of IT infrastructure, allowing for proactive problem detection and resolution. RMM tools enable tasks such as patch management, software deployment, and remote troubleshooting. Examples include ConnectWise Automate, Datto RMM, and SolarWinds N-central. In high-security environments, RMM tools can be used to enforce security policies, detect and respond to security incidents, and maintain compliance with regulatory requirements. However, RMM tools themselves can be a target for attackers, making their security a critical concern.
Security Considerations for CRM in High-Security Environments
Securing CRM systems in high-security environments requires a multi-layered approach that addresses various potential vulnerabilities.
Data Encryption
Encryption is the process of converting data into an unreadable format, protecting it from unauthorized access. Both data at rest (stored data) and data in transit (data being transmitted) should be encrypted. For CRM systems, this means encrypting data stored in the database, as well as data transmitted between the CRM system and user devices. Strong encryption algorithms, such as AES-256, should be used. Organizations should also implement key management practices to protect encryption keys from compromise. Considering these advancements in customer relationship management, The best CRM software in 2025 will likely focus on platforms offering enhanced AI-driven insights
.
Access Control
Access control mechanisms restrict access to CRM data and functionality based on user roles and permissions. The principle of least privilege should be followed, granting users only the minimum level of access required to perform their job duties. Multi-factor authentication (MFA) should be implemented for all users to add an extra layer of security beyond usernames and passwords. Regular reviews of user access rights are essential to ensure that permissions are appropriate and up-to-date.
Data Loss Prevention (DLP)
DLP solutions monitor and prevent sensitive data from leaving the CRM system without authorization. DLP policies can be configured to detect and block the transmission of sensitive data, such as credit card numbers or social security numbers, via email, file transfer, or other channels. DLP can also be used to monitor user activity and identify potential insider threats.
Regular Security Audits and Penetration Testing
Regular security audits and penetration testing are essential for identifying vulnerabilities in the CRM system and its surrounding infrastructure. Security audits assess the effectiveness of security controls and identify areas for improvement. Penetration testing simulates real-world attacks to identify exploitable vulnerabilities. The results of these assessments should be used to prioritize remediation efforts and improve the overall security posture. The implementation of a data-centric strategy, Driven Crm Enhances a business’s capacity to personalize customer interactions
Compliance Requirements
High-security environments often operate under strict regulatory requirements, such as HIPAA, PCI DSS, and GDPR. CRM systems must be configured and managed to comply with these regulations. This includes implementing appropriate security controls, maintaining audit logs, and responding to data breaches in a timely manner. Organizations should consult with legal and compliance experts to ensure that their CRM system meets all applicable regulatory requirements.
Security Considerations for RMM in High-Security Environments
RMM systems, while powerful tools for managing IT infrastructure, also present significant security risks if not properly secured. The inherent access and control capabilities of RMM make them attractive targets for attackers.
Secure RMM Infrastructure
The RMM server itself must be hardened against attack. This includes keeping the operating system and RMM software up-to-date with the latest security patches, implementing strong access controls, and restricting network access to the RMM server. The RMM server should be placed in a secure network segment with strict firewall rules.

Agent Security
RMM agents are installed on client endpoints to collect data and execute commands. These agents must be secured to prevent attackers from using them to gain unauthorized access to client systems. Strong authentication mechanisms should be used to verify the identity of RMM agents. Agents should be regularly updated to address security vulnerabilities. Organizations should also implement endpoint detection and response (EDR) solutions to monitor agent activity and detect malicious behavior.
Secure Remote Access
RMM systems provide remote access to client endpoints, which can be a significant security risk if not properly managed. Remote access should be restricted to authorized personnel and should be protected with strong authentication mechanisms, such as multi-factor authentication. Session recording and auditing should be enabled to monitor remote access activity and detect suspicious behavior. Organizations should also implement network segmentation to limit the impact of a compromised endpoint.
Patch Management
RMM systems can be used to automate patch management, which is a critical security control for preventing exploitation of known vulnerabilities. Organizations should establish a patch management policy that defines the frequency and scope of patching. Patches should be tested in a non-production environment before being deployed to production systems. RMM systems should be configured to automatically download and install security patches as soon as they are released.
Regular Security Assessments
The RMM system and its associated infrastructure should be regularly assessed for security vulnerabilities. This includes penetration testing, vulnerability scanning, and security audits. The results of these assessments should be used to prioritize remediation efforts and improve the overall security posture. Organizations should also stay informed about the latest security threats and vulnerabilities affecting RMM systems.
Best Practices for Integrating CRM and RMM in High-Security Environments
Integrating CRM and RMM can provide significant benefits, but it’s crucial to follow best practices to ensure that the integration does not compromise security.
Principle of Least Privilege
When integrating CRM and RMM, it’s essential to adhere to the principle of least privilege. Grant only the necessary permissions for each system to access the other. Avoid granting broad or unrestricted access, as this can create security vulnerabilities.
Secure API Integration
If CRM and RMM are integrated using APIs, ensure that the APIs are properly secured. Use strong authentication mechanisms, such as API keys or OAuth, to verify the identity of the calling application. Encrypt all data transmitted over the API. Implement rate limiting to prevent denial-of-service attacks. Regularly monitor API usage for suspicious activity.
Data Minimization
Only share the minimum amount of data necessary between CRM and RMM. Avoid sharing sensitive data that is not required for the integration to function. Implement data masking or anonymization techniques to protect sensitive data when it is shared.
Regular Security Audits
The integrated CRM and RMM environment should be regularly audited for security vulnerabilities. This includes reviewing access controls, API security, and data sharing practices. Penetration testing should be performed to identify exploitable vulnerabilities. Investing in the right resources can make a significant difference, as Crm Tools Improve customer relationship management processes
Incident Response Planning
Develop an incident response plan that addresses potential security incidents involving CRM and RMM. The plan should outline the steps to be taken in the event of a data breach, malware infection, or other security incident. The plan should be regularly tested and updated.
The Importance of a Holistic Security Approach
Securing CRM and RMM in high-security environments requires a holistic security approach that considers all aspects of the IT infrastructure. This includes implementing strong security controls at the network, endpoint, and application layers. Organizations should also invest in security awareness training for their employees to educate them about the latest security threats and best practices.
A holistic security approach also includes continuous monitoring and threat intelligence. Organizations should implement security information and event management (SIEM) systems to collect and analyze security logs from various sources. Threat intelligence feeds can be used to identify emerging threats and vulnerabilities. By continuously monitoring the environment and staying informed about the latest threats, organizations can proactively defend against cyberattacks.
In conclusion, CRM and RMM are valuable tools for organizations operating in high-security IT environments. However, their implementation and management must be carefully considered to avoid introducing security vulnerabilities. By following the best practices outlined in this article, organizations can leverage the power of CRM and RMM while maintaining the highest levels of security and compliance. Ultimately, a proactive and holistic security approach is essential for protecting sensitive data and ensuring the integrity of the IT infrastructure. To stay competitive, businesses are exploring new technologies, and understanding customer relationship management is key, Next Gen Crm offering advanced features and enhanced capabilities is becoming a critical investment
Frequently Asked Questions (FAQ) about CRM and RMM for High-Security IT Environments
What are the key security considerations when integrating a CRM (Customer Relationship Management) system with an RMM (Remote Monitoring and Management) platform in a high-security IT environment?
Integrating CRM and RMM in high-security environments requires careful planning. Data encryption, both in transit and at rest, is crucial to protect sensitive customer and system information. Robust access controls and multi-factor authentication (MFA) should be implemented to limit unauthorized access to both systems. Regular vulnerability scanning and penetration testing should be conducted to identify and address potential security weaknesses. Furthermore, incident response plans must be in place to effectively handle security breaches. Secure API integrations, adherence to compliance standards like HIPAA or PCI DSS (if applicable), and ongoing security awareness training for staff are also essential components for a secure CRM and RMM integration.
How can I ensure data privacy and compliance with regulations like GDPR or CCPA when using CRM and RMM solutions in an IT environment that handles highly sensitive data?
Protecting data privacy and ensuring compliance with regulations like GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) when using CRM and RMM solutions requires a multi-faceted approach. Data minimization, collecting only necessary data, is a fundamental principle. Implement consent management mechanisms for data collection and usage. Ensure transparent data processing policies are in place, clearly outlining how data is collected, used, and protected. Implement data anonymization and pseudonymization techniques where possible. Conduct regular data privacy impact assessments (DPIAs) to identify and mitigate privacy risks. Finally, establish clear procedures for handling data subject requests, such as access, rectification, and erasure requests, in accordance with applicable regulations. Choose CRM and RMM vendors that demonstrate a strong commitment to data privacy and security.
What are some best practices for implementing and configuring RMM tools within a highly regulated industry, such as healthcare or finance, to maintain security and regulatory compliance?
Implementing RMM tools in highly regulated industries like healthcare or finance demands strict adherence to security best practices and regulatory compliance. Start with a thorough risk assessment to identify potential threats and vulnerabilities. Implement role-based access control (RBAC) to restrict access to sensitive RMM features and data based on user roles. Configure RMM tools to enforce strong password policies and require MFA. Regularly review and update RMM configurations to align with evolving security threats and regulatory requirements. Implement audit logging and monitoring to track all RMM activities and detect suspicious behavior. Ensure RMM data storage and transmission comply with relevant regulations like HIPAA or PCI DSS. Implement endpoint security measures, such as anti-malware and intrusion detection systems, to protect managed devices. Finally, provide comprehensive training to IT staff on secure RMM usage and compliance requirements.
